Share this post
We saw in our previous article that artificial intelligences can be used to facilitate cyberattacks in a variety of ways, and that this type of attack is constantly on the increase. But AIs can also help companies to defend themselves, and thus ensure the security of their networks.
AI offers numerous advantages due to their data processing capabilities, machine learning and potential for analyzing and anticipating threats.
AI-assisted systems enable security teams to detect threats faster, and react more quickly to incidents.
So when malicious activity on a particular IP or endpoint is detected, it can automatically and instantly block user access to files.
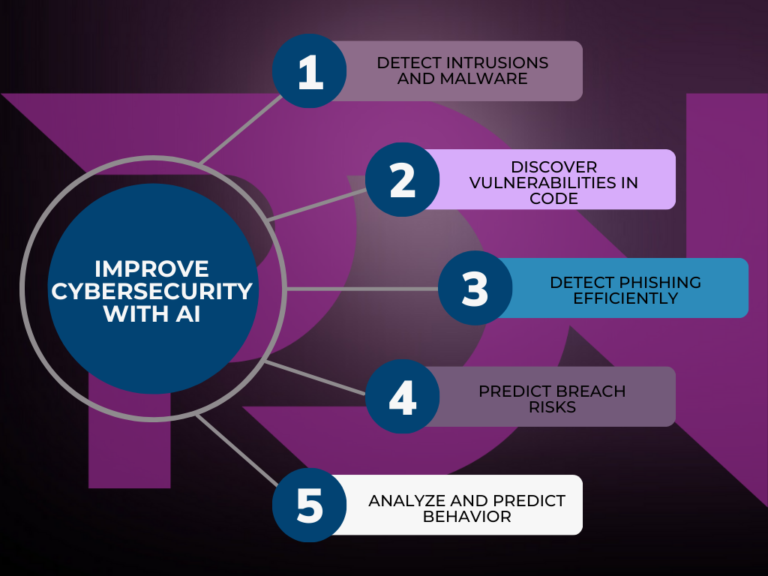
Here are the main methods used by AI to reinforce network security in companies:
While AI can be a powerful tool for strengthening cybersecurity initiatives, it does not replace traditional security approaches. In fact, it works best when used alongside traditional methods: combining AI with authentication, or biometric technology for example, can improve an organization’s defenses. An example might be the implementation of password managers: they automate the creation, updating and advice on the strength of chosen passwords. It is only by combining the two methods that corporate security can, in the age of AI, be truly maintained.
AI helps defenders to detect and identify the real threats in this data through pattern recognition in network traffic, malware indicators and user behavioral trends.
However, it’s important to note that AI is not free from limitations and risks. Adversaries can also use AI techniques to develop sophisticated attacks. Careful and considered use of AI in cybersecurity is therefore essential.

Join us at the beginning of October for our next article, in which we’ll discuss the relationships between the cloud and piracy.
In the meantime, if you have any content to protect – film, series, book, music album or software – please don’t hesitate to contact us. One of our account managers will be happy to help you find the formula best suited to your needs. We’ve been pioneers in cybersecurity and intellectual property protection for more than a decade, and our experts are here to help you protect your intellectual property.
Share this post